It is designed to accomplish the following purposes:
- To get unauthorized access to the owner computer and steal his/her credentials for doing criminal activities, for stealing money via online banking, to steal important documents etc.
- To hide malicious software like key loggers, viruses to harm the owner of computer.
- To utilize the computer as a Zombie Computer for performing any unethical activities like sending spam mails, for attacking others computer attached through the Home group etc.
Types of Rootkit Virus:
Persistent Rootkit Virus:
This Rootkit virus triggers every time the computer startup/reboots. It hides as a valid registry files and replicate action of valid windows registry files. It can’t be recognized easily and gets uploaded every time whenever the computers restart/reboot without any help from external factor. It remains in your computer registry even if the computer is rebooted.
Memory based Rootkit Virus:
This type of Rootkit virus lies in your computer memory. They occupy an unallotted portion of your computer RAM and remain until computer is shut down by the owner.
User Mode Rootkits:
In this case rootkits virus digs deep inside the operating system and stores itself in the system drive location and can’t be detected by the antivirus program. It escapes antivirus program detection by integrating itself with the antivirus program. When Antivirus program is initiated to scan the system, rootkit obstruct it and imitate the action of antivirus program and in result does not show any malware in result.
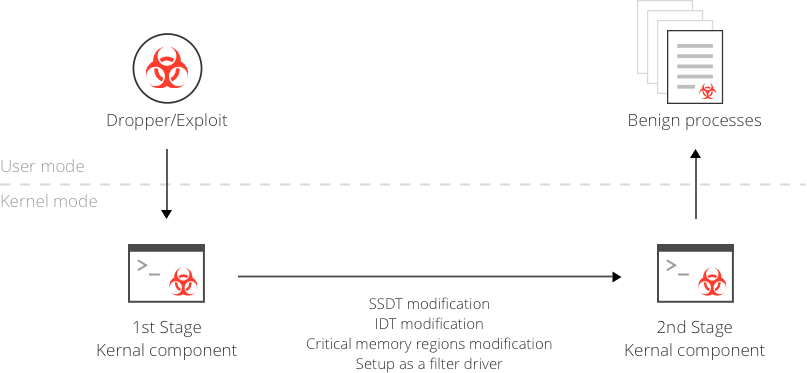
Kernel Mode Rootkits:
Kernel mode rootkits are more dangerous as compared to the other rootkits. This type of rootkits modifies the Kernel data structures by adding or replacing the existing code. This is one of the most lethal rootkits which can’t be detected by antivirus program as they operate at the same security level as the operating systems.
Firmware Rootkits:
Firmware rootkits affects the device attached by getting access to the device code and cease operation. You may have listen Mebromi rootkit which affects the graphic card of computer. This rootkit will reinstall itself when you restart your computer.
Boot kits:
Bootkits is the rootkit which is designed to contaminate the MBR (Master Boot Record) of the computer. It mainly affects the booting process and POST (Power on Self Test) of computer.
Hypervisor Rootkits:
This kind of rootkits is designed to affect the virtual machine setup. Hypervisor is a layer which is present between the physical layer and the virtual layer; it does not load itself when the computer restarts and become active when operating system is being prompted to initiate virtual machine. Its task is to exploit hardware virtualization and thus exploit system by intercepting hardware operation triggered by genuine operating system.
How to prevent Rootkits:
- One of the easiest ways to prevent your computer from rootkit is to create system restore points at regular interval.
- In most of the cases rootkit enters in computer through spam mails, it is always advised to avoid spam mails.
- It is always recommended to scan every external device before using it as they may contain harmful malwares.
- You must regularly update computer antivirus program from the genuine website of manufacturer. Apart from the genuine website of manufacturer don’t use antivirus which promises to provide full security these are traps created by the bad people to fulfill their evil intentions.
- Use Microsoft security essential security tools available on the Microsoft support website.
- The anti-virus program that you currently have installed no longer runs.
- PC reboot itself
- Error messages
- Your anti-virus stop working
- Your PC date and time keep changing to a wrong date even after you change CMOS battery
- PC slow down or run out of memory when you are only running one application
- Internet become slower
- Your computer locks up or fails to respond to common inputs
- Settings in Windows change without your permission
- You experience excessive network traffic or your network connect becomes slow or disconnected
Leave a Reply