 |
| Img.Credit: freedigitalphotos |
How often do you send emails, Word files or spreadsheets containing information that whilst not “top secret” it would be better that they were only accessed by your intended recipient? In the case of large file exchange or sharing this is normally achieved by uploading the file to a file sharing server and then letting the recipient know that it is there for them to download. Should we do more to protect these “shared files” from unauthorised access? Well in fact if these “file shares” are part and parcel to your companies business and contain any personal information you have a legal duty of care to ensure that their content is not revealed to the wider world.
Sending emails and files in “clear text” format is like sending your business letters on a post card. They can be intercepted and read by anyone who has the will to do so. Routinely our electronic ramblings are monitored by the various national security services at the very least.
So what can we do about it? We can obscure the content by means of encryption. By encrypting the content of an email or file we have effectively sealed it in an envelope. But surely this is going to be complicated and require the installation of software not only for me but also for my intended recipient, I hear you say. Well not necessarily. The new and emerging software solutions to this aged problem of providing robust encryption that everyone can use, simply without the need to understand all of the requisite complexities of random number generators, entropy and key pairs is proving that it is possible to bury these hitherto barriers within the program allowing a straightforward user interface to guide the user effortlessly through the maze in a couple of simple clicks.
If you will allow the pun, the “key” to this has been utilising a unique identifier for both sender and receiver. In this electronic age we all have such a thing, our email address! Imagine a system where a user’s email address is used in this way, the system can then generate key pairs associated with this address. These key pairs will be used to encrypt and decrypt any code the user may require protecting; emails, files, disks, thumb drives, CD-ROMs the list goes on. These encrypted portions of code can then be safely transported over any public or private network including the internet. They can even be stored on public servers awaiting collection by the recipient with the correct key/email address.
But how does the intended recipient’s email address work to decrypt the message? Easy because the data author or owner will know who they want to share that data with,so all that needs to happenis for the sender to supply the system with the email address of the intended recipient and it creates the necessary key pairs to enable encryption and decryption of the target code. These matching key pairs can be one-time pairs that will only apply to each data exchange further improving the security. Since each key pairing is only good for one exchange, if they were to be compromised it does not result in any future or past exchange being put at risk, clever!
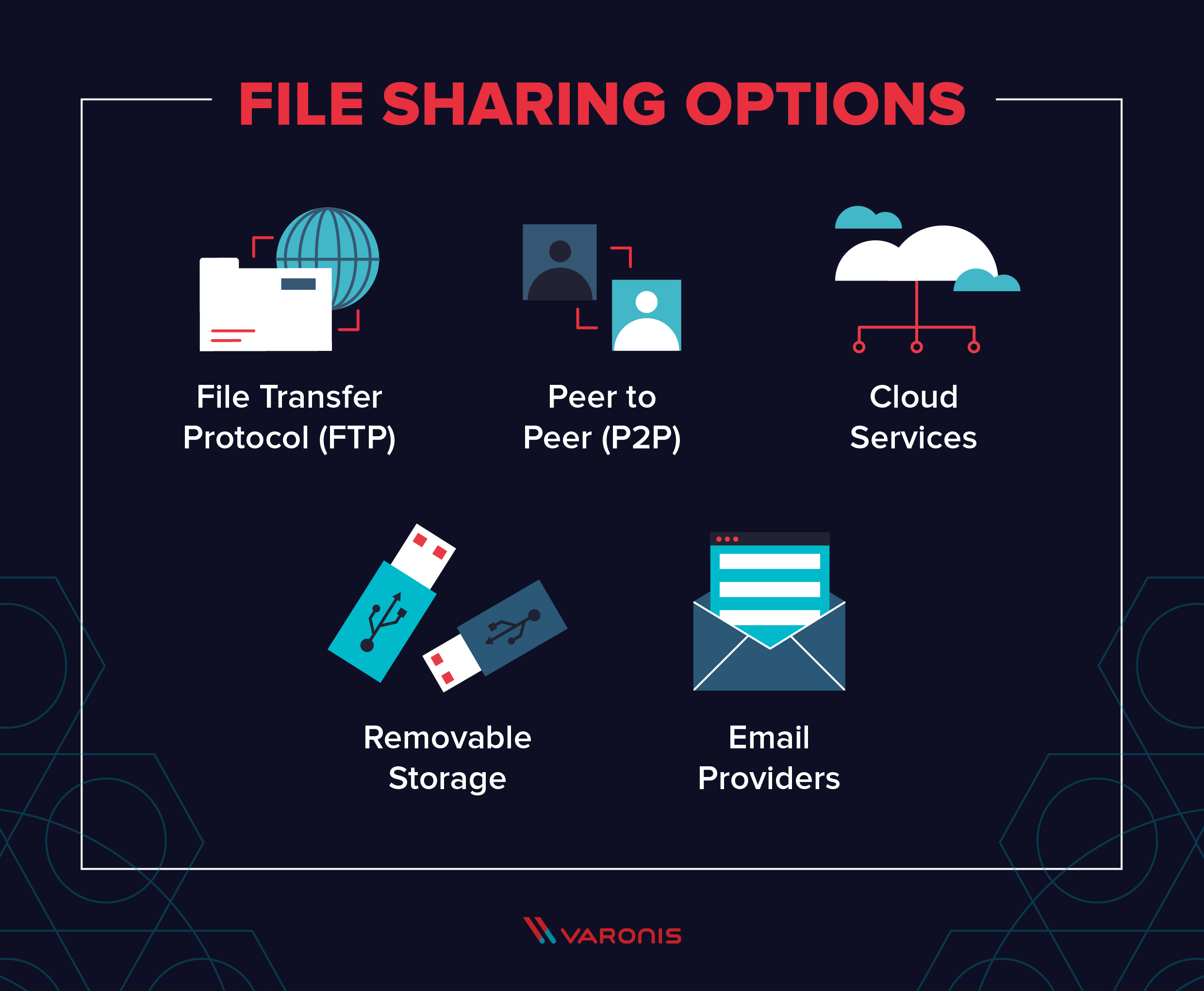
This type of system can be used to encrypt emails, their attachments, files copied to disks, thumb drives, CD-ROMs in fact any media. Making use of a cloud based repository you instantly have the ability to transfer large encrypted files with users anywhere on the planet. Or if you prefer by hand via whatever storage medium you wish to use.
One such system Egress’s Switch even allows you to make these secure file transfers with user’s who are not subscribers to the system. This allows you to make secure exchanges with your trading partners or friends without the need for them to make any installation of software on their systems. Superb!
Leave a Reply